Cybersecurity for Community Banks: The Threats That Actually Target You
Community banks are prime targets for ransomware, phishing, and vendor attacks — not despite their size, but because of it. Here's the threat landscape and what to do about it.
In August 2025, a ransomware group called Akira exploited a known vulnerability in a SonicWall VPN product at Marquis Software Solutions — a marketing and analytics vendor serving over 700 financial institutions. Within days, 80 banks and credit unions had been compromised. More than 823,000 customers had their names, Social Security numbers, account details, and dates of birth exposed. Marquis paid the ransom.
Not one of those 80 institutions was attacked directly. They were breached because their vendor was.
That’s the threat landscape for community banks in 2026. The attackers aren’t confused about who they’re targeting. They know exactly what they’re doing.
The “Too Small to Target” Myth Is Getting Banks Breached
The most dangerous assumption in community banking cybersecurity is that small institutions fly under the radar. They don’t. 90% of community banks now expect increasingly severe cyberattacks, according to recent industry surveys — and the threat actors behind those attacks have explicitly shifted toward smaller institutions because the return on effort is better.
Here’s the attacker’s calculus: a $500 million community bank has the same customer data as a branch of a regional bank, but a fraction of the security staff, smaller IT budgets, and often no dedicated security operations function. The attack surface is similar. The defenses are weaker. The payout — in stolen credentials, ransom payments, or data sold on criminal markets — is comparable.
Financial services breaches average $6.08 million per incident, according to IBM’s 2024 Cost of a Data Breach Report. That’s $1.2 million above the cross-industry average. And for a community bank operating on thin margins, a breach of that magnitude isn’t just painful — it’s potentially existential.
The Four Threats That Are Actually Hitting Community Banks
Skip the generic threat lists. These are the four attack types doing real damage to community financial institutions right now.
1. Ransomware via Third-Party Vendors
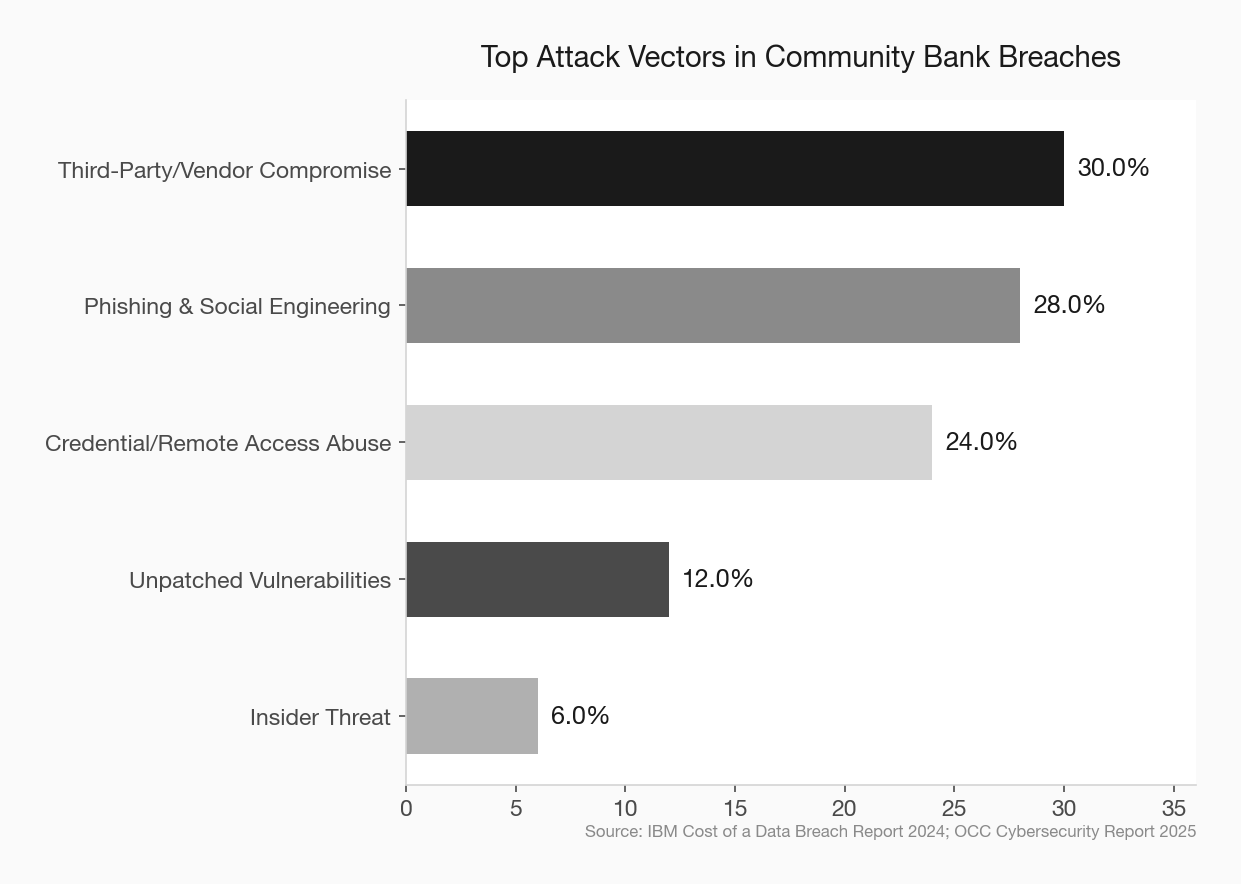
The Marquis breach isn’t an anomaly. 30% of all breaches now involve third parties, and the pattern is consistent: attackers identify a software or services vendor with weaker security than its bank clients, compromise that vendor, and use it as a backdoor into dozens of institutions simultaneously.
Community banks use dozens of vendors — cores, loan origination platforms, marketing software, compliance tools, HR systems. Each one is a potential entry point. And the vendor contracts many banks signed years ago include almost nothing about security standards, breach notification timelines, or liability.
The threat here isn’t just data loss. It’s operational disruption. If your loan origination system goes down during a ransomware attack on your vendor, you’re not closing loans. That’s a revenue event, not just a security event.
2. Phishing and AI-Enhanced Social Engineering
Phishing has always been the most common entry point for breaches. What’s changed is the quality of the attacks. AI-generated phishing emails are now grammatically flawless, contextually personalized, and often reference real internal details scraped from LinkedIn or your bank’s own website.
More alarming: deepfake voice clones targeting financial institutions surged 243% over the past year. Attackers are now calling bank employees — sometimes impersonating the CEO, sometimes a vendor contact — and instructing them to move funds, share credentials, or approve transactions. The calls sound real because they use audio cloned from publicly available recordings.
The majority of successful breaches still trace back to human error: a clicked link, a reused password, a wire transfer approved over the phone. No firewall stops a convincing phone call.
3. Credential Compromise and Unauthorized Remote Access
Remote access exploded during COVID and never fully contracted. Most community banks now have employees, contractors, and vendors accessing systems remotely on a regular basis. Every one of those remote connections is a potential entry point if credentials are weak or stolen.
Threat actors use phishing to harvest login credentials, buy them on criminal marketplaces, or brute-force them against VPN portals that have no lockout policy. Once inside, they move quietly — often remaining undetected for weeks before deploying ransomware or exfiltrating data.
The OCC’s 2025 Cybersecurity and Financial System Resilience Report specifically identifies compromised credentials through remote access solutions as a primary vector for ransomware and extortion campaigns against financial institutions.
4. Unpatched Systems and End-of-Life Technology
The Akira group’s attack on Marquis exploited CVE-2024-40766 — a critical vulnerability in SonicWall VPN products that had a known patch available. Marquis hadn’t applied it.
This is extraordinarily common. Community banks run on legacy infrastructure, and patch management is often inconsistent. End-of-life operating systems, unpatched network devices, and outdated core integrations create a vulnerability inventory that most institutions have never fully audited.
OCC examiners flagged IT lifecycle management and patch management as priority focus areas for 2025 examinations. That’s not bureaucratic box-checking — it’s a direct response to what they’re seeing in the field.
Where Community Banks Are Spending Wrong
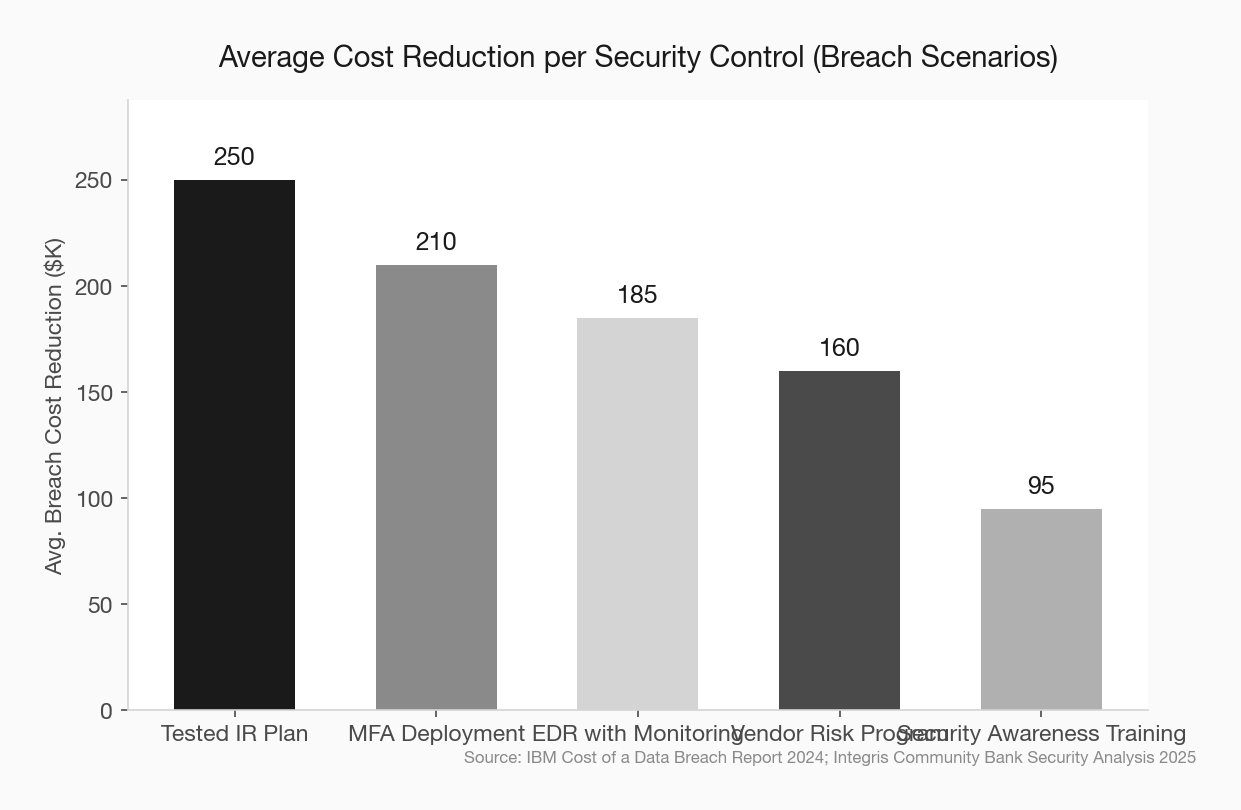
74% of bank executives say they don’t think their cybersecurity spending is effective. That’s a damning number, and it points to a specific problem: most community banks are spending on compliance artifacts — policies, assessments, annual training — rather than on controls that stop attacks.
A polished incident response policy that’s never been tested doesn’t stop ransomware. A penetration test report that sits in a binder doesn’t close the vulnerability it identified. Security awareness training delivered once a year doesn’t prepare an employee for an AI-generated deepfake call in real time.
The banks that are actually reducing risk are spending on a shorter list of higher-impact controls. The principle is protection per dollar, not coverage per line item.
The Controls That Actually Deliver
You don’t need a security operations center to meaningfully reduce your risk. You need to do five things well.
Multi-factor authentication on everything external. MFA on email, VPN, and remote desktop is the single highest-ROI control available. Valid account abuse — attackers using legitimate credentials — is involved in the majority of financial sector breaches. MFA doesn’t prevent credential theft, but it breaks the kill chain before damage is done. If you have employees or vendors accessing systems with just a username and password, that’s your most urgent fix.
Endpoint detection and response (EDR) with monitored alerting. Standard antivirus doesn’t catch modern attacks. EDR tools provide real-time visibility into suspicious activity on endpoints and can isolate a compromised device before ransomware spreads across the network. The key word is “monitored” — an EDR tool that generates alerts nobody reads isn’t protection.
Third-party vendor security assessments. Your vendors are your attack surface. Before the next contract renewal, ask each critical vendor for their SOC 2 Type II report, their most recent penetration test results, and their breach notification timeline. Vendors that can’t answer these questions are a liability. Build minimum security standards into new contracts.
Tested incident response. IBM’s research found that organizations with tested incident response plans reduce breach costs by nearly $250,000 per incident on average. Tabletop exercises — quarterly, not annually — where your team walks through a ransomware scenario do more for your actual security posture than most compliance activities.
Patching with documented timelines. Critical vulnerabilities — anything rated CVSS 9.0 or above — should be patched within 72 hours of a vendor release. High-severity vulnerabilities within 30 days. If your team can’t reliably meet those timelines, that’s a staffing or process problem worth solving before an examiner or an attacker finds the gap first.
What Regulators Are Looking For
The OCC’s 2025 examination priorities name cybersecurity as the top operational risk focus — and for the first time, examiners are specifically instructed to assess preventive controls, not just incident response and recovery capabilities.
That’s a meaningful shift. It means examiners are no longer satisfied with “we have a plan if something happens.” They want to see what you’re doing to stop something from happening. Preventive controls include MFA, vulnerability management, network segmentation, and access control reviews.
The FFIEC’s updated guidance and the GLBA Safeguards Rule amendments both push in the same direction: documented, tested, and continuously improved. Not a policy binder. A program.
GLBA Safeguards Rule compliance for community banks FFIEC cybersecurity assessment tool guide third-party vendor risk management for community banks
The Right Frame for This Investment
Community bank executives sometimes treat cybersecurity as a cost center — a compliance expense with no revenue upside. That frame is wrong, and it’s producing underinvestment.
Cybersecurity is credit risk management for your technology infrastructure. You wouldn’t skip credit underwriting because it doesn’t generate fee income. You do it because the alternative — an uncontrolled loss — is worse than the cost of the process.
A $6 million breach at a $500 million community bank is a capital event. It draws regulatory attention, triggers customer notification requirements, creates litigation exposure, and damages the trust relationships that are your core competitive advantage. The community banks that treat cyber risk with the same rigor they apply to credit risk are the ones that won’t be on next year’s breach list.
The Marquis attack affected 80 institutions that thought their vendor relationship was someone else’s problem. It wasn’t. And neither is yours.
AI tools for community bank security monitoring community bank technology vendor due diligence checklist